Permission Sets in IFS Cloud¶
The basis for Permission Sets in Aurena are grants given to Projections, Lobby Pages, Reports,Workflows and System Privileges. A Permission Set structure also makes it possible to grant Permission Sets to another set.
Permission Set Concepts, Expressions and Terms¶
Below are some concepts, expressions, and terms used to visualize and simplify the management of Permission Sets within IFS Cloud.
Limited Task User (LTU)¶
A LTU Permission Set only allows editing of the Projections that was delivered with the Permission Set. It can be granted to Users.
IFS Managed¶
Permission Sets with this badge cannot be changed in anyway except to add/remove Users. They are predefined by IFS and can be changed through special circumstances, for example in an update.
All Permission Sets prefixed with FND are considered as IFS Managed.
Projections and APIs¶
An API (application programming interface) is an access point for retrieving and posting data. It acts as a layer between the server and database on one side and a client on the other side. A web-API is accessible using a normal browser or other applications that can send http-requests.
The IFS Projection is a self-contained web-API which implements a defined business function. It describes data types, data sources and functions that can be utilized from the API. It is also the main point for security settings. It is in this layer that it is decided what data to return and which actions that are allowed.
The IFS Aurena client communicates with the database through Projections(APIs). The pages in IFS Aurena depend on Projections for retrieval of data and to perform actions. When granting access to a Projection all client pages using that projection will become available.
Access Level¶
Projections can have four different Access Levels in relation to a Permission Set: None, Read-Only, Custom and Full.




A Read Only Projection grant allows a User granted the Permission Set to read from all data sources and invoke all functions of a Projection. It also makes pages using the Projection available to the User.
A Full grant not only allows read access from data sources and functions but also create, update and delete access to all data sources of the projection and possibility to invoke all actions exposed by the projection.
A Projection can only be read-authorized as a single unit. A Projection that is granted, but has edited Action grants between Full and Read-Only is considered Custom
For example: A Projection that was granted Full had a Projection Action revoked. The Projection is now considered to have the Access Level Custom.
Access Level None indicates that the Projection is currently not granted to the Permission Set.
No of Pages¶
The number of pages depending on a Projection can vary. An indication is given by this badge that can have the following values
- Single Page Projection
- Multi Page Projection
- No Page Projection
Aurena Client Pages and Granting¶
Pages are granted through there respective Projection. When granting access to a Projection all client pages using that projection will become available.
TODO: should this even be here or better move it? Whether a page is available or not to a User granted the Permission Set is shown with a badge, Yes or No.
Badges for Currently Available and Will be Available will show up in Assistant when managing Projection Grants by Pages. These indicate what the state of the pages will be after completing the Assistant.
Not all pages are shown in the navigator menu, like the Manage by Page assistant. Some pages are only available through commands or other workflows. The badge In Navigator shows whether a page is in the navigator menu or not.
Lobby Pages¶
Information on Lobby Pages can be found here.
Reports¶
Information on Reports can be found here:
System Privileges¶
Read more about the concept of System Privileges here.
Permission Set Structure¶
The total permissions of a Permission Set is the sum of permissions granted directly to the Permission Set and all permissions granted indirectly through other Permission Sets granted to the Permission Set.
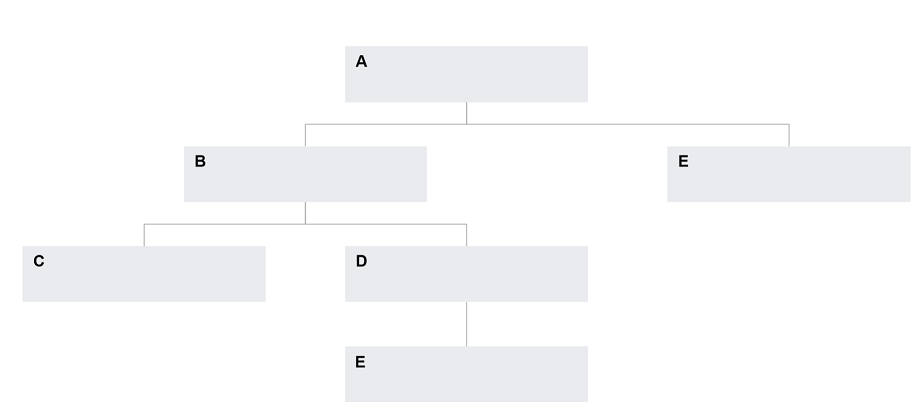
In the above example Permission Set A would include all the permissions from Permission Sets B, C, D and E. It is not possible to create a circular grant, where a Permission Set in someway gets granted to itself.